How is WPA3 more secure than WPA2?
There is a lot of buzz in the industry about WPA3 and, especially, after the scare we had with WPA2 (see our blog post: krack-hack-is-wpa2-dead /). So, how is WPA3 more secure then WPA2?
WPA3 is promising to improve security in multiple ways, over WPA2
If you have 802.1X/EAP/RADIUS (WPA2-Enterprise) configured (correctly) you can be quite smug, you have security. But all those PSK (WPA2-Personal) networks out there have a few challenges. With PSK, the PMK (the head honcho, top dog, key) is calculated from the PSK (basically, the PSK is chopped in half). So, every time anyone logs onto your wireless network, they are using the same seed key. Now, this is not as bad as everyone using the same key, but it’s still not good.
Anyway, not to worry, because you regularly change the PSK every 30 days, or so, and you always change it when anyone leaves the company, right? Umm, right? Erm, probably not. This tends to be the reality of PSK.
Remember, a hacker can capture your traffic from your network, take it home, and work on it offline. They can use a dictionary attack, or a brute force attack to guess your PMK. The PMK, remember, is half of the PSK which, in turn, is calculated from a mixture of your SSID and the passphrase you used. So, even though the 4-way handshake gives us unique keying per-station per-connection (by using random numbers and including the MAC-address), we are all still starting off with the same seed key.
WPA3 solves the open network issue
WPA3 is looking to address your local Coffee Shop’s security issues. “Whaaaaaat?” you may ask. Well, every time you use the free wireless at your local Coffee Shop, or airport, or plane/bus etc. you may be a lot less secure than you think. (See our blogpost “ Only With an ‘s’ ”).
Anytime you have “no security” or “open authentication only” running, you basically have NO security. So, if there is no PSK and no 802.1X/EAP/RADIUS configured, you are basically sending all your traffic unencrypted. Assuming you are using HTTPS, and TLS IMAP/SNMP this may not be as scary as it first seems, but it sure should make you sit up and say “What?”
To emphasize, if you are working on an “open” network, there is no 4-way handshake, so you have no encryption.
Some folks just don’t “get” security. So, the Wi-Fi Alliance (WFA) are working on our behalf to help us with this in WPA3. The aim of the certification is to help secure Wi-Fi, even though people may not turn on any security. This part of the puzzle is provided by Opportunistic Wireless Encryption or OWE which is very similar to SAE which is explained below.*
The first thing the WFA is doing, is to include Simultaneous Authentication of Equals (SAE) technology first covered in 802.11s. There is a great overview on this in the CWSP book (by “the two Dave’s and Bryan”): https://amzn.to/2OayIYU
You really should own this book – and actually read it.
For the real geeks amongst you, I am including a share, which I provide in class, of a good set of introductions to Diffie Helman (DH), and Eliptic Curve Diffie Hellman (ECDH). This can be found at the following location: http://bit.ly/ncx-enhanced-security
SAE is based on the Dragonfly Key Exchange. Effectively, it is based around DH or EDCH. If that is too much acronym-ing for you then, put simply, it “magically” creates a secure key, by interacting mathematically between two remote stations. You can see this in Diagram 1 (yes, I know it’s bad, but I knocked it up real quick. I’ll make it look pretty, later). Note: the SAE exchange takes place in place of the standard Authentication exchange.
Diagram 1: Flow of SAE
WPA3 enforces a minimum of 128-bit security
WPA3 enforces a minimum of 128-bit security, allows 192-bit (and optionally 256-bit) encryption, and forbids the use of TKIP. WPA3 also mandates the use of 802.11w PMF (it must be available, but it can be made optional).
Initially, it will run in transition mode, which will allow WPA2 and WPA3 on the same SSID but, eventually, they are hoping to have WPA3 mandatory without WPA2 support, once enough vendors and clients support it. This is not unusual, because this is what happened with the transition to WPA2, until 2014, when the Wi-Fi alliance said “no more TKIP in WPA2”.
Using SAE has many hidden benefits. As well as making our networks more secure, it also stops hackers capturing our traffic and taking them away to work on. The SAE protocol makes any capture useless, unless you are a part of the SAE exchange. This is still true, even if your PSK is compromised! (This is known as “forward security”.) This makes an SAE PMK immune to offline dictionary attacks.
PSK will be demoted to be the authentication piece, with SAE becoming the main engine to create encryption keys.
WPA3 makes IoT much easier
WPA3 is promising to make the onboarding of IoT and IoE “things” much easier using a simple QR Code function.
All of this is going to be invisible to end users but, of course, requires AP and client vendors to start to support the certification.
* Update – September 2018
OWE was originally intended to be a part of WPA3, but it never made it in the final release, and is now being worked on as a separate Certification. See here:
https://www.wi-fi.org/news-events/newsroom/wi-fi-certified-enhanced-open-delivers-data-protection-in-open-wi-fi-networks
https://tools.ietf.org/html/rfc8110
(Oh no, he posted an RFC…. )
)
Also see these great audio-cast from our friends at CTS on OWE:
http://www.cleartosend.net/aruba-networks-demos-owe-mfd3/
And this great presentation on WPA3 and OWE by Chuck from Aruba – a demo they did at Mobility Field Day 3:
https://youtu.be/O233UgBX0tM
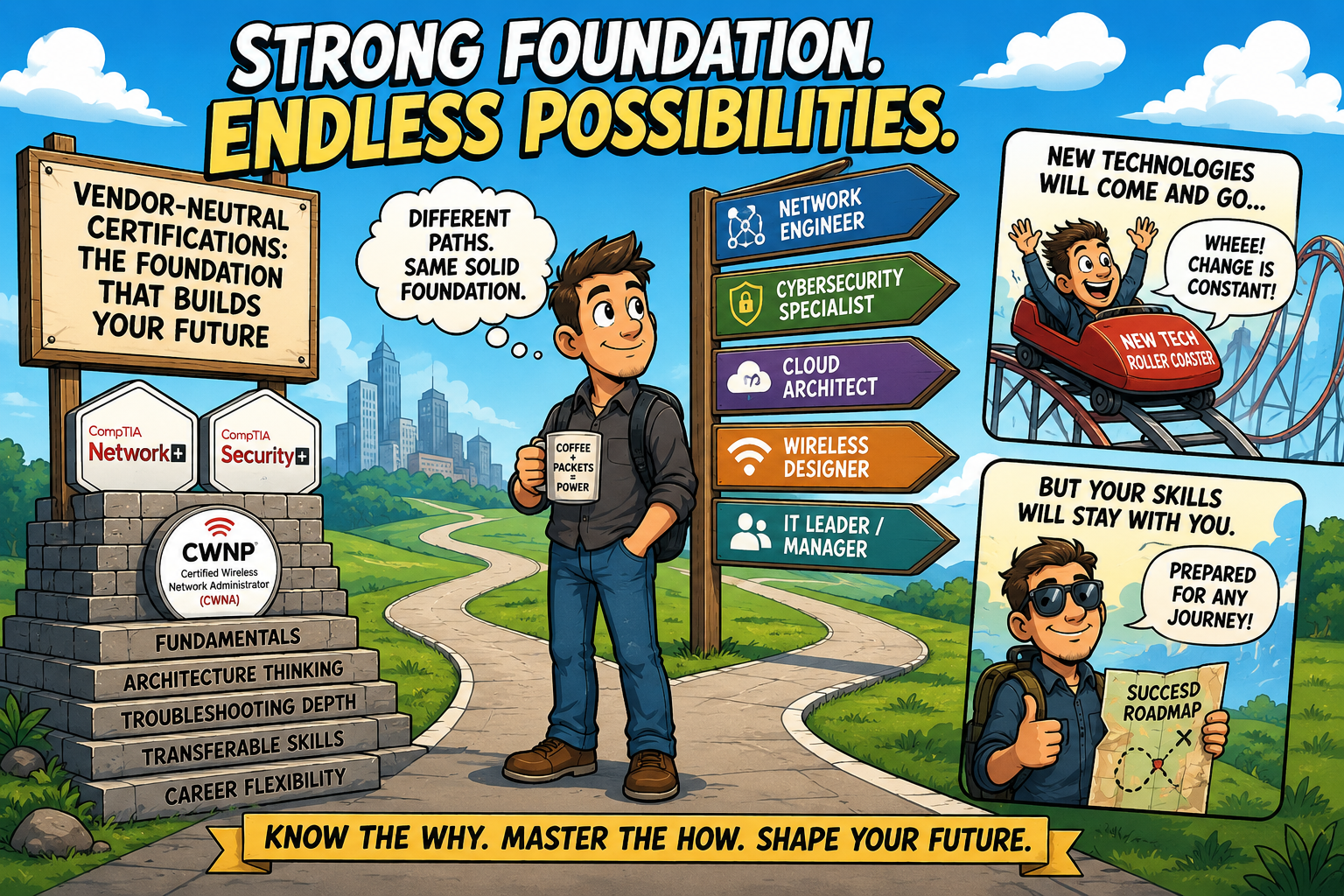
If you are looking to make your mark in the IT Industry, then NC-Expert offers excellent training courses aimed at relevant IT industry certifications – contact us today to get started.
NC-Expert Blog